It’s affecting our banks. It’s hurting our healthcare organizations. It’s in our pipelines! Let's break it down for those of you who keep meaning to Google the specifics, but to be honest it's all you can do to remember to look up what a "yeet" is.
 What Is Ransomware?
What Is Ransomware?
Ransom malware (ransomware) prevents users from accessing their system or files and demands ransom payment in order to regain access. In some cases, the attackers will also threaten to release or leak the data if the ransom is not paid.
When Did This Become A Thing?
In 1989. This is an interesting story, but to be brief: floppy disks were mailed to 20,000 AIDS researchers in 90 countries under the guise of an AIDS risk survey from biologist Dr. Joseph Popp. Upon loading the disk, researchers’ computers were infected with a trojan horse virus (a type of malware that works exactly how it sounds - you think you’re downloading a fancy wooden horse, but really it’s a fancy wooden horse PLUS some malware). Poetically, the virus laid dormant until the 90th boot, when an angry red page replaced the users’ screen demanding payment of $189 (paid via snail mail) to unlock their files. Popp’s program was relatively rudimentary - it simply changed the users’ filenames and extensions. Once the encryption tables were known, the files could be restored. Popp was arrested, and while he claimed the profits from his crime were intended for AIDS research, no one believed him, and that’s still a crime. He was declared mentally unfit for trial - something about curlers in his beard and condoms on his nose. I think he sounds fun.
What Does Ransomware Look Like?
Scareware
The mildest of the bunch, scareware is named as such because it feeds on your fears. Anyone who has seen the flashing “Warning! This computer is infected!” pop-up has witnessed scareware. Usually it provides a phone number for “tech support,” where you can pay some criminals $80 to put additional malware on your computer. In this case, your data has likely been untouched, provided that you do not click anything or call anyone and give them your private data. If presented with scareware, ctrl-alt-delete yourself back to safety and run an anti-virus scan from your trusted AV.
Screen lockers
Slightly more worrisome than scareware is lock-screen ransomware. In this scenario, you might start up your computer to see a full-sized window accompanied by an FBI or US Department of Justice seal stating that criminal activity has been detected on your device and you must pay a fine. It probably doesn’t need to be said, but this is not how the FBI or the Department of Justice would contact you if they suspected you of illegal activity. While annoying, screen lockers can be bypassed without paying the attackers, provided you have a bit of technical experience.
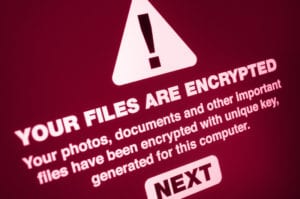
Encrypting ransomware
Now you're in a pickle. In this type of attack, your locally stored files - and sometimes cloud backups, too - are taken hostage and encrypted. Payment, usually in the ballpark of a few hundred, but sometimes thousands (or, for larger companies, millions) of dollars is demanded in return for decryption and return. Crypto-ransomware uses the same sophisticated technology that encrypts our conversations, banking transactions, and military communication, so unscrambling isn’t possible without paying the ransom. Even worse, there’s no guarantee the criminals will hold up their end of the deal in the event you do pay.
How do I get it?
Most of the time, it comes as an attachment or link in a carefully crafted phishing email. It can also be spread through "drive-by downloading," which can happen through no fault of your own. You may visit a legitimate site that has been compromised by malicious code. The malicious code hopes to identify software weaknesses on machines and web browsers to determine which systems are vulnerable.
How Do I Keep My Stuff Safe?
- Most importantly, maintain offline backups. Many ransomware programs will look for connected backups, so this “offline” bit is important. This way if they take your data, you can restore from your backup. Test your backups periodically to be sure everything is working.
- Keep your programs and operating system up to do date. Those patches are there for a reason - often that reason is security vulnerabilities.
- Be suspicious of your emails. Even if the alias looks like it’s from someone you know, check the actual email address - is it correct?
- Use an ad-blocker. Drive-by download attacks often use advertisements to upload infections. An ad blocker can help limit your exposure.
- Use a reputable antivirus. Bitdefender is good (even if we hate them right now), but our favorite is Malwarebytes OneView.
Lastly, Some Good News
If you’re feeling down about all this crime, or that you didn’t get into the cybercriminal game because it’s great money and you love a hoodie, here’s some good news: In 2013, a man turned himself in to the police after being deceived by “FBI” ransomware claiming to know of illegal activity on his computer. It turned out there was in fact child pornography on the man’s computer, and the man was arrested. Silver linings! The world is an A-OK place, guys.
If you have concerns about how to accomplish any of the above recommended actions, please reach out to your friendly specialists at Patient Computer Help, Inc. to set up a consultation.
Patient Computer Help, Inc. assists people with their Macs and PCs in the Chagrin Falls and Ohio City areas.